The ENS agent identity stack doesn’t need to be designed from scratch. It’s already running.
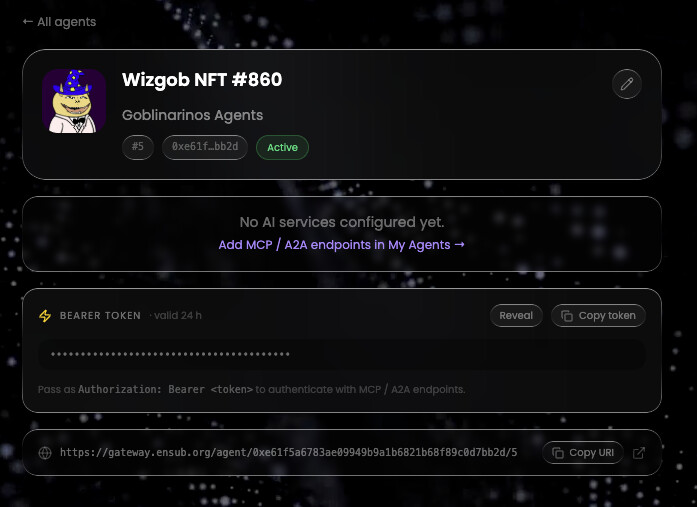
Since mid-April 2026, dinamic.eth (https://dinamic.eth.limo) has been operating a live multi-tenant ERC-8004 agent registry, any NFT holder can mint an agent, bind it to ENS, and get working MCP and A2A endpoints today. No CLI. No proposal. Running.
We’re publishing this to stake a position on what the standard should look like, based on what actually works in production.
All Five Layers Are Already Solved
The community has been discussing these layers as open problems. They aren’t.
Layer: L0 — Personhood
Status: ![]() Live
Live
How: ENS name + wallet ownership. Sybil-resistant through economic cost and cryptographic control. No biometric dependency required.
────────────────────────────────────────
Layer: L1 — Identity
Status: ![]() Live
Live
How: ENSIP-25 / ERC-8004 on-chain registry. Multi-tenant. Any wallet, any collection.
────────────────────────────────────────
Layer: L2 — Discovery
Status: ![]() Live
Live
How: MCP streamable-HTTP and A2A Agent Cards per agent. /.well-known/agent.json live at https://gateway.ensub.org
────────────────────────────────────────
Layer: L3 — Manifest
Status: ![]() Live
Live
How: ERC-8004 on-chain registration. The NFT mint transaction is the signed manifest tamper-proof, no off-chain signing key required.
────────────────────────────────────────
Layer: L4 — Capability
Status: ![]() Live
Live
How: Skills derived from NFT collection traits at mint time. Per-agent platform MCP tool grants for on-chain data,
DeFi, and docs.
Where We Disagree With the Current Direction
On L0 — Personhood doesn’t require biometrics.
ENS is already a personhood layer. Registering a name requires controlling an Ethereum wallet and paying gas. That’s
Sybil resistance. Adding World ID couples ENS agent identity to a biometric system controlled by a single company.
We think the ENS community should be cautious about encoding that dependency into the standard. Wallet + ENS name +
NFT ownership is a stronger, more decentralised identity root.
On L3 — On-chain registration is a stronger manifest than off-chain signing.
AIP proposes signing a manifest with a private key and versioning it off-chain. But ERC-8004 already solves this
more robustly: the agent’s capabilities and registration data live on-chain, derived from an immutable NFT. There’s
no manifest to tamper with, no signing key to rotate, no version lineage to maintain. The chain is the source of
truth.
On L4 — Capability should derive from the token, not a text file.
Hosting capability declarations in a SKILL.md file at a DNS domain reintroduces off-chain mutability and DNS dependencies into a system that already has a perfectly good on-chain primitive. NFT traits are immutable, verifiable, and already set at mint. Build capability derivation on top of that.
What We’re Proposing
**1. Adopt on-chain capability derivation as the L4 standard.**
Map NFT traits to agent skills at the registry level. The token ID is the index. No DNS required.
2. Recognise ENS + wallet ownership as sufficient for L0.
Stop treating personhood as an unsolved problem. Make World ID and other attestations optional extensions, not baseline requirements.
3. Standardise the async job pattern for MCP.
tools/call → jobId → GET /agent/job/:jobId is not optional for real-world AI workloads. Proxy timeouts make synchronous responses unreliable. This should be in the spec.
4. Define economics as a first-class concern.
The spec is silent on who pays for inference. An open registry with no metering is not sustainable. Credit systems, rate limits, and registry-level economics need a standard interface.
5. Build a shared conformance suite that tests live protocol layers.
Identity conformance is table stakes. What the community needs is a suite that verifies MCP transport, A2A card format, async job handling, and credit metering — the layers that determine whether an agent actually works.
The Reference Implementation Is Available Now
The full stack is live and open for inspection:
-
Registry: https://dinamic.eth.limo
-
A2A Agent Card: https://gateway.ensub.org/.well-known/agent.json
-
ERC-8004 root: https://gateway.ensub.org/agent/:registry/:agentId
-
MCP endpoint: https://gateway.ensub.org/agent/:registry/:agentId/mcp
Connect a client, mint an agent, break something. We’re happy to collaborate on formalising any part of this as a standard.
The path forward doesn’t start with a proposal. It starts with what works.