@raffy I think you changed addr() in normalization/resolver page recently? & I see addr(60) in your example page too.
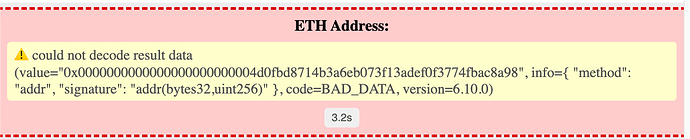
There are two addr() returns (address) & addr(node, 60) returns(bytes) for ETH address… As addr() is from original resolver our wildcard/offchain data is using addr() format but our data is stored in addr(60) space *as address instead of bytes(address)…
So I was wondering if we should skip using addr()/address and always use addr(60)/bytes format?